Proposal
Serverless Log Management & Analytics Pipeline
Unified AWS Serverless Solution for Scalable Log Processing
1. Executive Summary
The Serverless Log Management & Analytics Pipeline is designed to provide centralized log ingestion and analysis for diverse applications, running on AWS. It supports high‑volume log streams from multiple sources, with scalability to handle millions of events per day. The pipeline leverages AWS Serverless services to deliver real‑time classification, optimized long‑term storage, and cost‑efficient analytics. Access control is managed through AWS Identity and Access Management (IAM), ensuring secure usage across designated teams.
SERVERLESS LOG MANAGEMENT & ANALYTICS PIPELINE 1.Executive Summary Dự án tập trung xây dựng một hệ thống quản lý và phân tích nhật ký (log) tập trung, sử dụng hoàn toàn kiến trúc Serverless trên nền tảng điện toán đám mây AWS. Hệ thống được thiết kế để giải quyết bài toán tiếp nhận dữ liệu log khổng lồ từ nhiều ứng dụng khác nhau, xử lý phân loại thời gian thực và lưu trữ tối ưu cho mục đích phân tích dài hạn. 2.Problem Statement What’s the Problem Log ứng dụng nằm rải rác trên nhiều máy chủ, gây khó khăn cho việc giám sát tập trung. *The Solution Hệ thống triển khai sử dụng cloudwatch agent gửi log lên vào cloudwatch , từ cloud watch sẽ gửi vào đường ống dữ liệu (SQS) tiếp nhận ổ định thông qua lambda , từ sqs gọi aws lambda để phân loại dữ liệu theo thời gian thực: lưu trữ metadata tại DynamoDB (Hot Data) để truy vấn nhanh và đẩy payload thô lên Amazon S3 (Cold Data) phục vụ phân tích lâu dài bằng Amazon Athena và Aws glue,nếu có lỗi sẽ báo qua SNS. Đồng thời triển khai một app đăng kí tài khoản sử dụng cognito và iam đăng kí người dùng vào sns. Với amazon athena thì triển khai một app sử dụng ec2 để đăng nhập và truy vấn dữ liệu log 3.Solution Architecture
2. Problem Statement
What’s the Problem?
Application logs are scattered across multiple servers, making centralized monitoring and analysis difficult. This fragmentation leads to inefficiencies in troubleshooting, delayed insights, and challenges in maintaining system reliability.
The Solution
The pipeline leverages AWS CloudWatch Agent to collect logs and forward them to CloudWatch, which then streams data into Amazon SQS for stable ingestion. AWS Lambda processes messages from SQS in real time, classifying logs and storing metadata in DynamoDB (Hot Data) for fast queries, while raw payloads are archived in Amazon S3 (Cold Data) for long‑term analytics using Amazon Athena and AWS Glue. Error notifications are sent via Amazon SNS. User access is managed through Amazon Cognito and IAM, enabling secure registration and subscription to SNS alerts. For advanced queries, an EC2‑based application provides controlled access to Athena for log analysis.
Benefits and Return on Investment
This solution establishes a unified, serverless log management system that reduces operational overhead and improves visibility across distributed applications. Real‑time classification accelerates troubleshooting, while cost‑efficient storage in S3 supports scalable analytics. By automating ingestion and alerting, teams save significant time compared to manual log collection. Monthly costs remain minimal under AWS’s serverless pricing model, with long‑term ROI achieved through improved reliability, reduced downtime, and streamlined maintenance.
3. Solution Architecture
The pipeline employs a fully serverless AWS architecture to centralize log ingestion, processing, and analytics across distributed applications. Logs are collected via CloudWatch Agents, streamed through Amazon SQS for reliable delivery, and processed by AWS Lambda for real‑time classification. Metadata is stored in DynamoDB for fast queries, while raw payloads are archived in Amazon S3 for long‑term analysis with Athena and Glue. Notifications are handled by SNS and CloudWatch Alerts, ensuring timely responses to anomalies. User registration and access control are managed through Cognito and IAM, with ECS applications integrated into the system for secure usage. The architecture is detailed below:
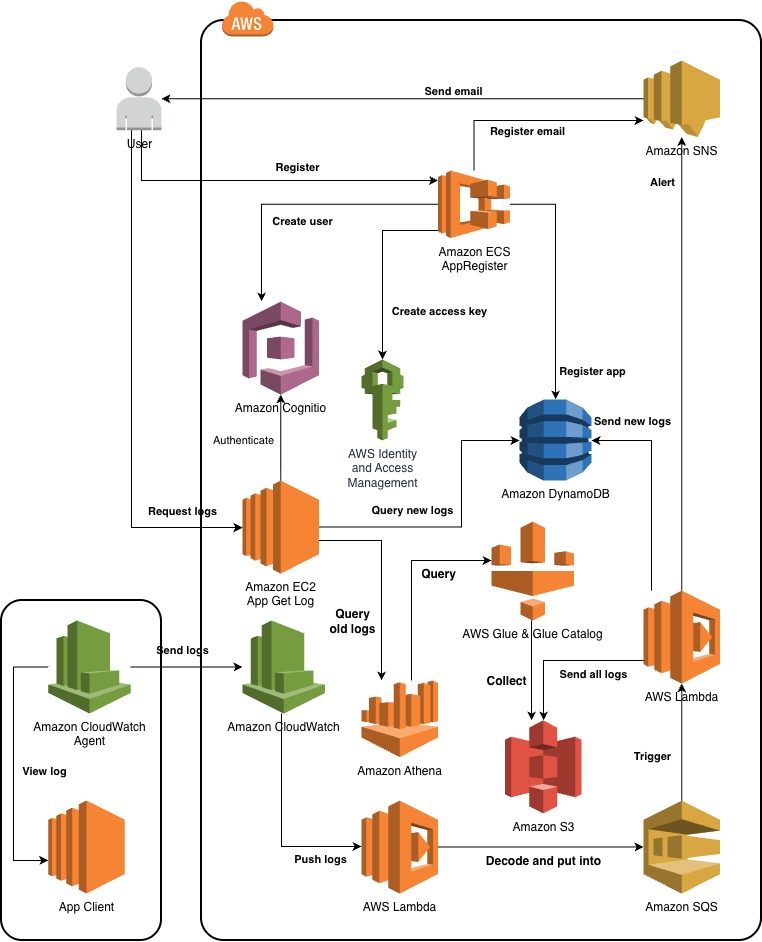
AWS Services Used
- Amazon Cognito: Manages user registration and authentication.
- AWS IAM: Provides secure access keys and role‑based permissions.
- Amazon ECS: Registers applications and associates them with user accounts.
- Amazon DynamoDB: Stores user metadata and registration details.
- Amazon CloudWatch: Centralizes log collection and monitoring.
- CloudWatch Agent: Collects logs from EC2/ECS applications.
- Amazon SQS: Ensures reliable, asynchronous log ingestion.
- AWS Lambda: Processes and classifies logs in real time.
- Amazon S3: Stores raw logs for long‑term analysis.
- AWS Glue & Glue Catalog: Organizes and transforms log data.
- Amazon Athena: Enables SQL‑based queries on historical logs.
- Amazon SNS: Sends alerts and notifications for anomalies.
- CloudWatch Alerts: Detects unusual patterns and triggers responses.
Component Design
- Identity & Access Layer: Cognito handles user registration, IAM enforces permissions, and ECS/DynamoDB store user and app metadata.
- Monitoring & Logging Layer: CloudWatch Agent collects logs from applications, which are centralized in CloudWatch.
- ETL & Analytics Layer: Lambda processes logs, Glue organizes data, Athena enables queries, and S3 provides scalable storage.
- Notification & Response Layer: SQS queues events, SNS distributes alerts, and CloudWatch triggers anomaly detection.
4. Technical Implementation
Implementation Phases
- Architecture Design: Define serverless log pipeline and AWS service integration (Week 1-2).
- Cost Estimation & Optimization: Use AWS Pricing Calculator to forecast expenses and adjust design (Week 3-4).
- System Setup & Integration: Configure CloudWatch Agents, Lambda functions, and Glue jobs (Week 5-6).
- Testing & Deployment: Validate ingestion, classification, and alerting workflows; deploy to production (Week 7-8).
Technical Requirements
- Log Sources: Applications running on EC2/ECS with CloudWatch Agents.
- Data Pipeline: CloudWatch → SQS → Lambda → DynamoDB/S3.
- Analytics: Athena queries on S3 data, Glue ETL for structured analysis.
- Access Control: Cognito for user authentication, IAM for permissions.
- Notifications: SNS and CloudWatch Alerts for anomaly detection.
5. Timeline & Milestones
Project Timeline
- Pre‑Implementation (Week 1-2): 2 week for planning and reviewing existing log collection methods.
- Implementation (Week 3-8):
- Week 3-4: Study AWS services and configure CloudWatch Agents for applications.
- Week 5-6: Design and adjust the pipeline architecture, integrate Lambda, SQS, DynamoDB, and S3.
- Week 7-8: Implement, test, and launch the full system with Glue jobs and Athena queries.
- Post‑Launch: Up to 1 year for optimization, monitoring, and scaling log ingestion.
6. Budget Estimation
You can find the budget estimation on the AWS Pricing Calculator.
Infrastructure Costs
- AWS Services:
- AWS Lambda: $0.00/month (1,000 requests, 512 MB).
- Amazon S3 Standard: $0.20/month (10 GB logs, 3,000 requests, 2 GB scanned).
- Data Transfer: $0.03/month (2 GB inbound, 2 GB outbound).
- Amazon DynamoDB: $0.10/month (metadata queries).
- Amazon SQS: $0.05/month (50,000 messages).
- Amazon SNS: $0.02/month (alerts & notifications).
- Amazon CloudWatch: $0.15/month (log ingestion & monitoring).
- AWS Glue ETL Jobs: $0.05/month (2 DPUs).
- AWS Glue Crawlers: $0.07/month (1 crawler).
- Amazon Athena: $0.10/month (SQL queries on S3).
- AWS Lambda: $0.00/month (1,000 requests, 512 MB).
Total: ~$0.77/month, ~$9.24/12 months. No hardware costs are required since the system leverages AWS infrastructure.
7. Risk Assessment
Risk Matrix
- Log Volume Spikes: High impact, medium probability.
- Service Misconfiguration: Medium impact, medium probability.
- Cost Overruns: Medium impact, low probability.
- Access Control Breach: High impact, low probability.
Mitigation Strategies
- Log Spikes: Use SQS buffering and Lambda auto‑scaling.
- Misconfiguration: Manage infrastructure with CloudFormation/CDK templates.
- Cost: Enable AWS budget alerts and optimize Glue/Athena queries.
- Access Control: Enforce Cognito + IAM policies, enable MFA for users.
Contingency Plans
- Pipeline Failure: Temporarily store logs locally on EC2/ECS instances.
- Cost Issues: Roll back configurations using CloudFormation templates.
- Access Breach: Disable IAM keys, trigger SNS alerts, and restore permissions.
8. Expected Outcomes
Technical Improvements
The pipeline enables real‑time log ingestion and analytics, replacing fragmented manual collection across multiple servers. It provides centralized visibility, faster troubleshooting through metadata queries in DynamoDB, and scalable long‑term storage in S3. SQL‑based queries via Athena streamline analysis, while automated alerts through SNS and CloudWatch reduce downtime.
Long‑Term Value
The system establishes a one‑year foundation of log data for operational research and performance optimization. It is reusable for future projects, serving as a model for serverless data pipelines. By minimizing manual monitoring and leveraging AWS’s pay‑as‑you‑go model, the solution ensures cost efficiency, scalability, and reliability for enterprise‑level applications.